ADExplorer Exporting Quick Tip

Working with ADExplorer as a Red Teamer is really useful for seeing the whole domain in a single snapshot that can be looked at offline. There is minimal tooling out there for parsing ADExplorer or even exporting things and the closest I could find was ADEGrab but sadly it wasn't working, so a work around solution is to use Process Hacker 2 to grab strings from memory for ADExplorer. The steps below detail how to do it. Thanks to Mantis for the suggestion to try PH2.
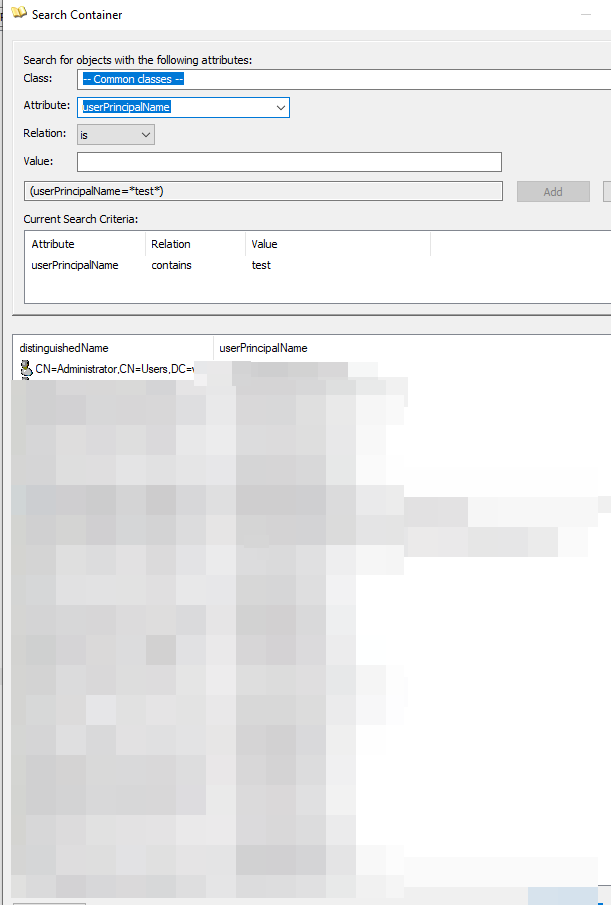
- Open ADExplorer and perform the search you want to do:
- Next open Process hacker and find the ADExplorer process:
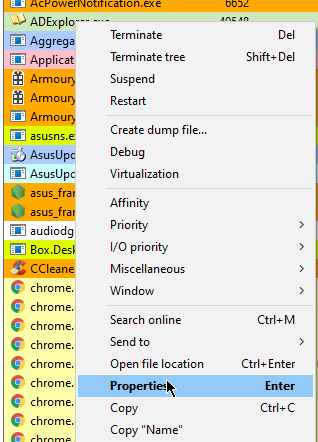
Navigate to properties -> memory -> strings
set a minimum length, it defaults to 10 characters
tick, private, image, mapped and click OK
Select filter then enter what you want to filter by 'contains', in this case I'm going to use the domain.com:
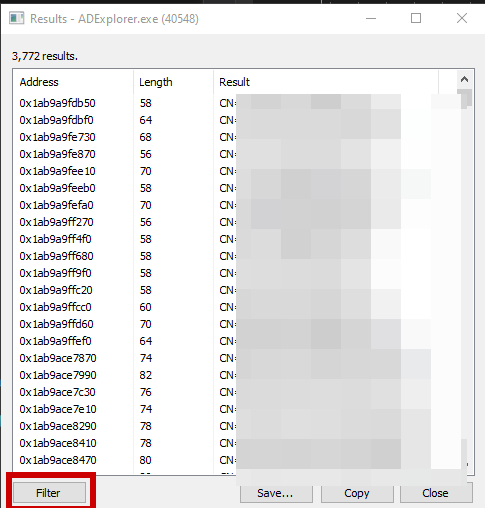
click save or copy then you can filter out the text till you get the list of users you want.
Go fourth and hack folks!
